Last week, we looked at why a solid backup strategy is so important to the health and well-being of your website. Just like a good homeowner’s insurance policy will restore your belongings and help you rebuild your house in case of theft or fire, backups will allow you to get up and running again as quickly as possible in case something catastrophic happens to your website.
Aside from a good insurance policy, you likely have an alarm system and smoke detectors to prevent problems from becoming severe in the first place. The same holds true for your website. There are a multitude of threats out there, and while it’s impossible to go through and present an exhaustive, comprehensive list of potential security vulnerabilities, this article will show you some of the most common risks and how to mitigate them.
Is WordPress Insecure?
Let’s take on one myth up front: the conception that WordPress is inherently less secure than other website platforms out there. This is simply not true. While admittedly, WordPress has suffered some high-profile security vulnerabilities over its nearly fourteen year existence, so have many systems. It’s the nature of computing. Any popular platform, from Windows to WordPress, is going to attract its fair share of hackers, crackers, and ne’er-do-wells. But there are steps you can take to keep those rogue players from mucking up your little corner of the interwebs.
Brute Force Attacks
Probably the number one type of attack I deal with in managing WordPress sites (and this is true for all administration-based content management systems), is that of brute force attacks. This is an attack in which a hacker attempts to break into your system by trying a number of username and password combinations, attempting to gain access. Often times these are not the efforts of a single individual, banging away at potential access credentials on his or her own, but rather a scripted attack that will automate the attempt from a number of other compromised systems around the globe. Here are some steps to take to prevent them from succeeding:
- Always use a strong, gibberish password that you don’t use anywhere else. In recent releases, WordPress has helped with this by offering a strong password generator and displaying warnings against overly simplistic and commonly-guessed ones.
- Never use the username “admin”. Once upon a time, “admin” was WordPress’ default suggestion for the first username that would go into the system. Hackers know this, and know that there are many, many systems out there that still use this username as their all-powerful administrator account, figuring that their chances of success have improved by 50%.
- Use two-factor authentication. By requiring an extra step, often using an app installed on your smartphone, it becomes impossible to log into your websites admin by username and password alone. Google Authenticator has become the de facto standard for 2FA on a number of online services, and there is a plugin for WordPress that uses it as well. (I’ll have more to say about 2FA and WordPress in an upcoming post.)
- Always put your admin behind HTTPS. I’ll get deep into HTTPS and its benefits another day, but trust me when I say you should definitely do this. While not strictly a brute force attack strategy, any data that is sent over a non-HTTPS connection is easily readable by anybody who happens to be listening to that traffic. In other words, if you log into your WordPress site over a non-secure HTTP URL, those keys to your administration are going over publicly-accessible wires in plain text. Not good.
Attacks Through Compromised Code
Software is only as secure as its code. Vulnerabilities lurk in poorly-coded themes and plugins, and sometimes even in core itself. Most of the time, these problems aren’t intended to allow hackers in; quite the contrary. But when they’re discovered, word immediately spreads of the vulnerabilities that were found, and the bad guys get to work. Hence the term zero-day exploit.
This is where vigilance is especially important. There are a number of WordPress security services out there that send out newsletters when important vulnerabilities are discovered. Sucuri is one of my favorites, but some other popular ones include iThemes and WordFence. Subscribe to their blogs or follow them on Twitter to be kept up-to-date on the latest happenings in WordPress security. We’ll dive deeper into keeping your software updated in a later post in this series, but monitoring when your plugins and core need to be updated should be part of any comprehensive security monitoring program.
Install a Good Security Monitoring Plugin (or Two, or Three…)
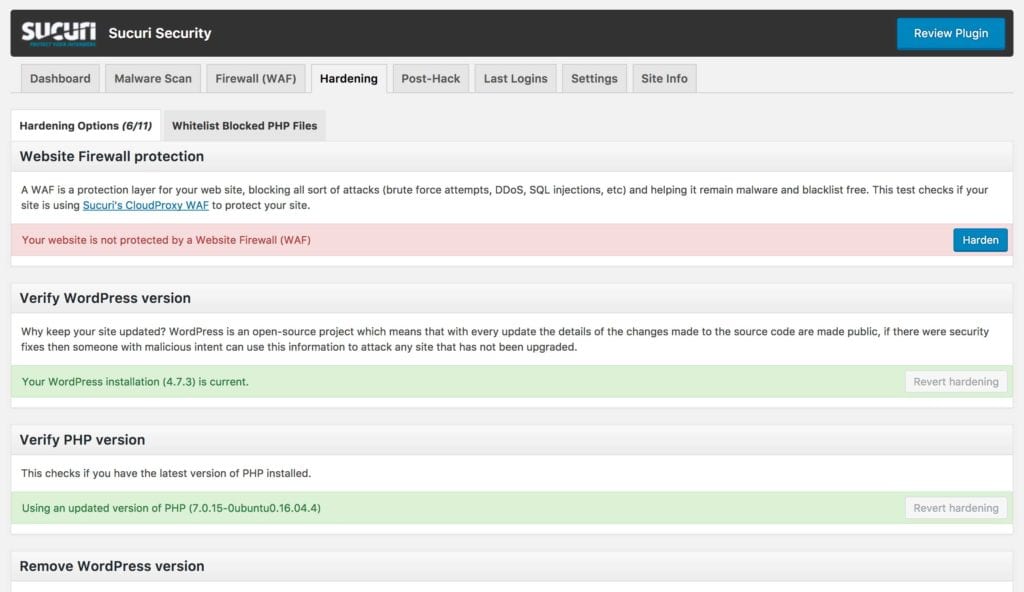
I already talked about Sucuri, iTheme, and WordFence; all three of those services offer free plugins on the WordPress plugin repository that let you monitor the security of your site without requiring a monthly subscription fee. These plugins will offer recommendations on how to “harden” your website; that is, easy steps you can take to make your WordPress a less vulnerable target. They will also log login attempts, and notify you if they suspect a brute force attack is in the works. All three of those services also offer paid services that include firewalls and other advanced security features. Compare their plans and find the one that matches your needs with your price point, but keep in mind: A good security service is worth its price in terms of saving your website after a hack.
There are a number of other plugins you can install that will help you monitor what’s going on with your site when you’re not looking. Limit Login Attempts is an extremelypopular plugin that will block out login access to your website after three failed attempts from a particular URL in a short time frame. Such patterns of failed attempts are classic signs that your site is under a brute force attack. (The WordPress plugin repository warns that this plugin hasn’t been updated in over two years, but it’s okay to go ahead and install it anyway.)
Security in an Insecure World
Forewarned is forearmed, and the recommendations in this post are just the tip of the iceberg in securing your WordPress website. In my next post, we’ll look at the best way to manage core, plugin, and theme updates: a vital step in keeping your WordPress site secure and healthy.
Need Help?
Just like most people call in an expert to install their home security system, you don’t have to maintain your WordPress website all on your own. Taupecat Studios can help. We offer monthly maintenance plans to take the tasks of backups, security monitoring, software updates, and uptime monitoring off of your plate so you can focus on your business. Get in touch and let us know how we can help.
