It can sometimes be confusing for non-technical website owners to understand all the layers of a website. Domain registrars, name servers, hosting providers, and software each play integral roles. In this article, we explain the technical layers of a WordPress website stack and how they relate to each other.
Author: Tracy Rotton
Earlier this week, Elon Musk changed Twitter’s logo from its iconic bird to… an X. Not just any ol’ X, but Unicode character U+1D54F. It’s all—purportedly—part of his ongoing rebranding efforts to create an “everything” app, one central hub for communication, shopping, entertainment and more. How well (or not) this hub concept succeeds is the […]
Lately, it feels like the WordPress powers that be aren’t appreciating the consequences of their actions.
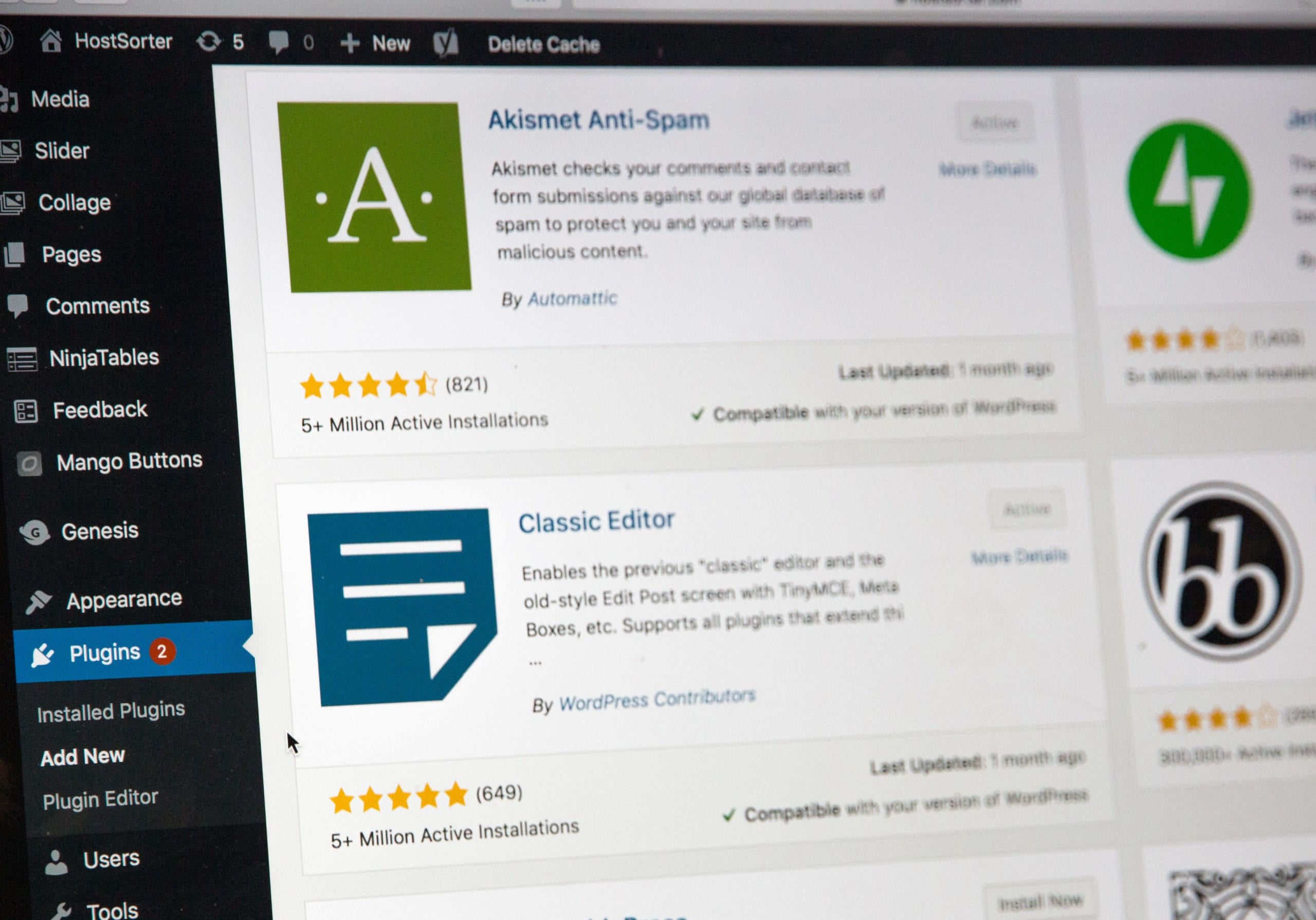
Should clients be allowed to install plugins on their WordPress websites when they’re already working with a maintenance provider? On its face, this might seem a simple question, but it’s actually one that’s filled with nuance and “it depends…” type scenarios. This post was inspired by this tweet: My reply: (The way Pantheon locks down […]
Today I’m previewing a new video series on how to use the new Sass module system. The first video, on Tooling, is available on YouTube now. Subsequent videos on using the new module system and other recent improvements in Sass will be following in the coming weeks. Transcript Welcome. In this video, we’ll be setting […]
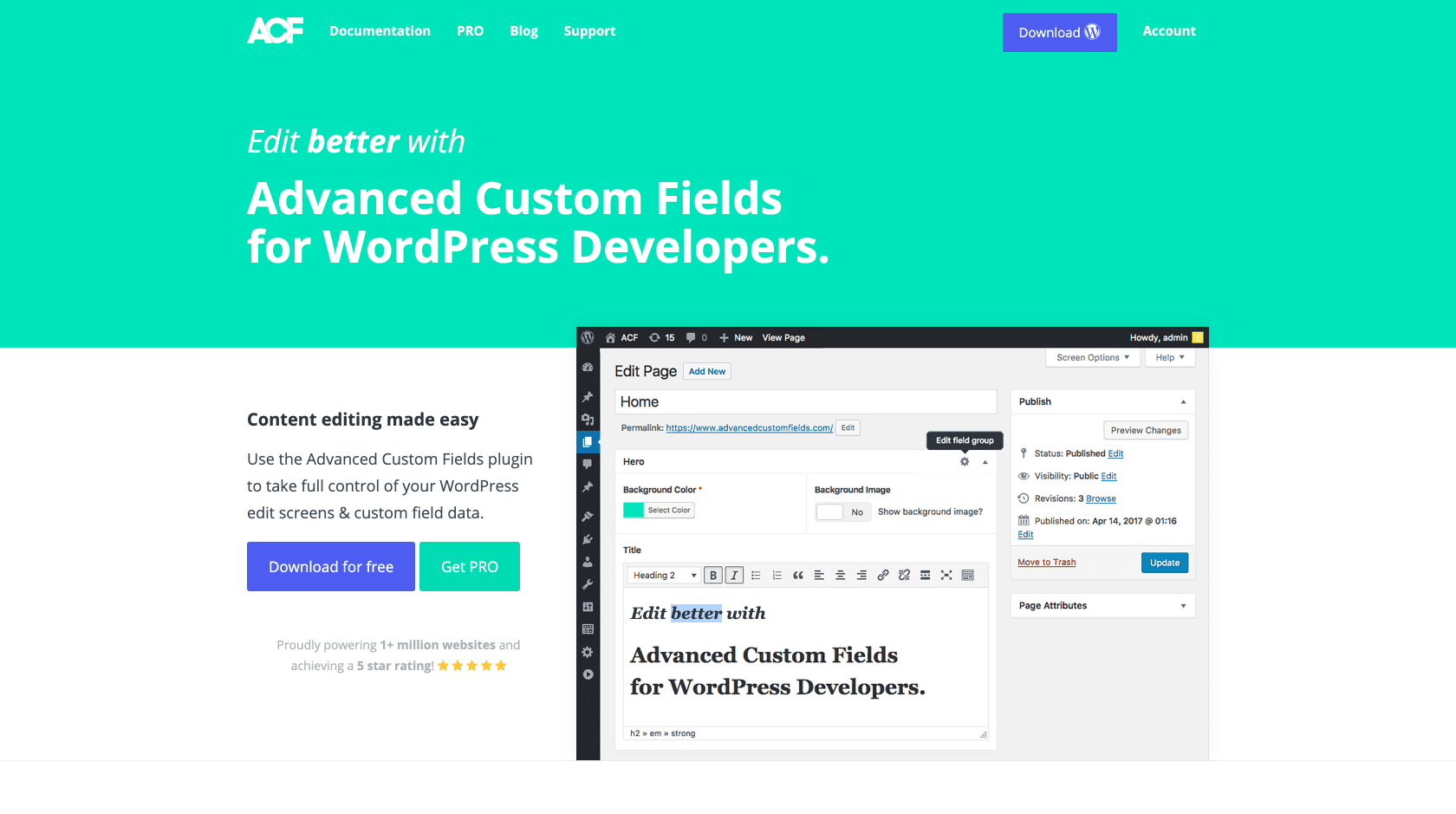
What happens when a much-loved plugin announces a price increase? In the case of Advanced Custom Fields PRO, a whole lot more ❤️.